-->
- Microsoft Autoupdate Mac Won't Update
- Microsoft Auto Updater For Mac
- Microsoft Autoupdate Mac Download Windows 10
Download Mac App Remover. When installed, Microsoft AutoUpdate creates files in several locations. Generally, its additional files, such as preference files and application support files, still remains on the hard drive after you delete Microsoft AutoUpdate from the Application folder, in case that the next time you decide to reinstall it, the. This update to Microsoft AutoUpdate for Mac is part of Microsoft's continued effort to provide the latest product updates to customers. To receive future product updates, you must install this update.
Important
Get the latest updates available for your computer's operating system, software, and hardware. We will scan your computer and provide you with a selection. Excel for Microsoft 365 for Mac Word for Microsoft 365 for Mac Outlook for Microsoft 365 for Mac PowerPoint for Microsoft 365 for Mac Office 2019. Will update automatically. But you can also manually download the updates: Open the Mac App Store from. AutoUpdate, see Update history for Office for Mac. Need help with Microsoft AutoUpdate? If AutoUpdate isn’t doing the job and you continue losing the package file downloaded by it, feel free to go to this Microsoft webpage and download the update directly. Alternatively you can, of.
Microsoft Autoupdate Mac Won't Update
Welcome to Microsoft Defender for Endpoint, the new name for Microsoft Defender Advanced Threat Protection. Read more about this and other updates here. We'll be updating names in products and in the docs in the near future.
Applies to:
This page will guide you through the steps you need to take to set up macOS policies in Jamf Pro.

You'll need to take the following steps:
Step 1: Get the Microsoft Defender ATP onboarding package
In Microsoft Defender Security Center, navigate to Settings > Onboarding.
Select macOS as the operating system and Mobile Device Management / Microsoft Intune as the deployment method.
Select Download onboarding package (WindowsDefenderATPOnboardingPackage.zip).
Extract
WindowsDefenderATPOnboardingPackage.zip.Copy the file to your preferred location. For example,
C:UsersJaneDoe_or_JohnDoe.contosoDownloadsWindowsDefenderATPOnboardingPackage_macOS_MDM_contosojamfWindowsDefenderATPOnboarding.plist.
Step 2: Create a configuration profile in Jamf Pro using the onboarding package
Locate the file
WindowsDefenderATPOnboarding.plistfrom the previous section.In the Jamf Pro dashboard, select New.
Enter the following details:
General
- Name: MDATP onboarding for macOS
- Description: MDATP EDR onboarding for macOS
- Category: None
- Distribution Method: Install Automatically
- Level: Computer Level
In Application & Custom Settings select Configure.
Select Upload File (PLIST file) then in Preference Domain enter:
com.microsoft.wdav.atp.Select Open and select the onboarding file.
Select Upload.
Select the Scope tab.
Select the target computers.
Select Save.
Select Done.
Step 3: Configure Microsoft Defender ATP settings
Use the following Microsoft Defender ATP configuration settings:
- enableRealTimeProtection
- passiveMode
Note
Not turned on by default, if you are planning to run a third-party AV for macOS, set it to
true.- exclusions
- excludedPath
- excludedFileExtension
- excludedFileName
- exclusionsMergePolicy
- allowedThreats
Note
EICAR is on the sample, if you are going through a proof-of-concept, remove it especially if you are testing EICAR.
- disallowedThreatActions
- potentially_unwanted_application
- archive_bomb
- cloudService
- automaticSampleSubmission
- tags
- hideStatusMenuIcon
For information, see Property list for Jamf configuration profile.
Save the file as
MDATP_MDAV_configuration_settings.plist.In the Jamf Pro dashboard, select General.
Enter the following details:
General
- Name: MDATP MDAV configuration settings
- Description:<blank>
- Category: None (default)
- Distribution Method: Install Automatically(default)
- Level: Computer Level(default)
In Application & Custom Settings select Configure.
Select Upload File (PLIST file).
In Preferences Domain, enter
com.microsoft.wdav, then select Upload PLIST File.Select Choose File.
Select the MDATP_MDAV_configuration_settings.plist, then select Open.
Select Upload.
Note
If you happen to upload the Intune file, you'll get the following error:
Select Save.
The file is uploaded.
Select the Scope tab.
Select Contoso's Machine Group.
Select Add, then select Save.
Select Done. You'll see the new Configuration profile.
Step 4: Configure notifications settings
Microsoft Auto Updater For Mac
These steps are applicable of macOS 10.15 (Catalina) or newer.
Download
notif.mobileconfigfrom our GitHub repositorySave it as
MDATP_MDAV_notification_settings.plist.In the Jamf Pro dashboard, select General.
Enter the following details:
General
- Name: MDATP MDAV Notification settings
- Description: macOS 10.15 (Catalina) or newer
- Category: None (default)
- Distribution Method: Install Automatically(default)
- Level: Computer Level(default)
Select Upload File (PLIST file).
Select Choose File > MDATP_MDAV_Notification_Settings.plist.
Select Open > Upload.
Select the Scope tab, then select Add.
Select Contoso's Machine Group.
Select Add, then select Save.
Select Done. You'll see the new Configuration profile.
Microsoft Autoupdate Mac Download Windows 10
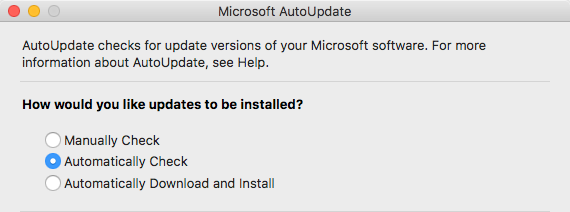
Step 5: Configure Microsoft AutoUpdate (MAU)
Use the following Microsoft Defender ATP configuration settings:
Save it as
MDATP_MDAV_MAU_settings.plist.In the Jamf Pro dashboard, select General.
Enter the following details:
General
- Name: MDATP MDAV MAU settings
- Description: Microsoft AutoUpdate settings for MDATP for macOS
- Category: None (default)
- Distribution Method: Install Automatically(default)
- Level: Computer Level(default)
In Application & Custom Settings select Configure.
Select Upload File (PLIST file).
In Preference Domain enter:
com.microsoft.autoupdate2, then select Upload PLIST File.Select Choose File.
Select MDATP_MDAV_MAU_settings.plist.
Select Upload.
Select Save.
Select the Scope tab.
Select Add.
Select Done.
Step 6: Grant full disk access to Microsoft Defender ATP
In the Jamf Pro dashboard, select Configuration Profiles.
Select + New.
Enter the following details:
General
- Name: MDATP MDAV - grant Full Disk Access to EDR and AV
- Description: On macOS Catalina or newer, the new Privacy Preferences Policy Control
- Category: None
- Distribution method: Install Automatically
- Level: Computer level
In Configure Privacy Preferences Policy Control select Configure.
In Privacy Preferences Policy Control, enter the following details:
- Identifier:
com.microsoft.wdav - Identifier Type: Bundle ID
- Code Requirement: identifier 'com.microsoft.wdav' and anchor apple generic and certificate 1[field.1.2.840.113635.100.6.2.6] /* exists */ and certificate leaf[field.1.2.840.113635.100.6.1.13] /* exists */ and certificate leaf[subject.OU] = UBF8T346G9
- Identifier:
Select + Add.
Under App or service: Set to SystemPolicyAllFiles
Under 'access': Set to Allow
Select Save (not the one at the bottom right).
Click the
+sign next to App Access to add a new entry.Enter the following details:
- Identifier:
com.microsoft.wdav.epsext - Identifier Type: Bundle ID
- Code Requirement: identifier 'com.microsoft.wdav.epsext' and anchor apple generic and certificate 1[field.1.2.840.113635.100.6.2.6] /* exists / and certificate leaf[field.1.2.840.113635.100.6.1.13] / exists */ and certificate leaf[subject.OU] = UBF8T346G9
- Identifier:
Select + Add.
Under App or service: Set to SystemPolicyAllFiles
Under 'access': Set to Allow
Select Save (not the one at the bottom right).
Select the Scope tab.
Select + Add.
Select Computer Groups > under Group Name > select Contoso's MachineGroup.
Select Add.
Select Save.
Select Done.
Step 7: Approve Kernel extension for Microsoft Defender ATP
In the Configuration Profiles, select + New.
Enter the following details:
General
- Name: MDATP MDAV Kernel Extension
- Description: MDATP kernel extension (kext)
- Category: None
- Distribution Method: Install Automatically
- Level: Computer Level
In Configure Approved Kernel Extensions select Configure.
In Approved Kernel Extensions Enter the following details:
- Display Name: Microsoft Corp.
- Team ID: UBF8T346G9
Select the Scope tab.
Select + Add.
Select Computer Groups > under Group Name > select Contoso's Machine Group.
Select + Add.
Select Save.
Select Done.
Step 8: Approve System extensions for Microsoft Defender ATP
In the Configuration Profiles, select + New.
Enter the following details:
General
- Name: MDATP MDAV System Extensions
- Description: MDATP system extensions
- Category: None
- Distribution Method: Install Automatically
- Level: Computer Level
In System Extensions select Configure.
In System Extensions enter the following details:
- Display Name: Microsoft Corp. System Extensions
- System Extension Types: Allowed System Extensions
- Team Identifier: UBF8T346G9
- Allowed System Extensions:
- com.microsoft.wdav.epsext
- com.microsoft.wdav.netext
Select the Scope tab.
Select + Add.
Select Computer Groups > under Group Name > select Contoso's Machine Group.
Select + Add.
Select Save.
Select Done.
Step 9: Configure Network Extension
As part of the Endpoint Detection and Response capabilities, Microsoft Defender ATP for Mac inspects socket traffic and reports this information to the Microsoft Defender Security Center portal. The following policy allows the network extension to perform this functionality.
Note
JAMF doesn’t have built-in support for content filtering policies, which are a pre-requisite for enabling the network extensions that Microsoft Defender ATP for Mac installs on the device. Furthermore, JAMF sometimes changes the content of the policies being deployed.As such, the following steps provide a workaround that involve signing the configuration profile.
Download
netfilter.mobileconfigfrom our GitHub repository to your device and save it ascom.microsoft.network-extension.mobileconfigFollow the instructions on this page to create a signing certificate using JAMF’s built-in certificate authority
After the certificate is created and installed to your device, run the following command from the Terminal from a macOS device:
From the JAMF portal, navigate to Configuration Profiles and click the Upload button.
Select Choose File and select
microsoft.network-extension.signed.mobileconfig.Select Upload.
After uploading the file, you are redirected to a new page to finalize the creation of this profile.
Select the Scope tab.
Select + Add.
Select Computer Groups > under Group Name > select Contoso's Machine Group.
Select + Add.
Select Save.
Select Done.
Step 10: Schedule scans with Microsoft Defender ATP for Mac
Follow the instructions on Schedule scans with Microsoft Defender ATP for Mac.
Step 11: Deploy Microsoft Defender ATP for macOS
Navigate to where you saved
wdav.pkg.Rename it to
wdav_MDM_Contoso_200329.pkg.Open the Jamf Pro dashboard.
Navigate to Advanced Computer Searches.
Select Computer Management.
In Packages, select + New.
In New Package Enter the following details:
General tab
- Display Name: Leave it blank for now. Because it will be reset when you choose your pkg.
- Category: None (default)
- Filename: Choose File
Open the file and point it to
wdav.pkgorwdav_MDM_Contoso_200329.pkg.Select Open. Set the Display Name to Microsoft Defender Advanced Threat Protection and Microsoft Defender Antivirus.
- Manifest File: Select Upload Manifest File.
Options tab
Keep default values.Limitations tab
Keep default values.Select Save. The package is uploaded to Jamf Pro.
It can take a few minutes for the package to be available for deployment.
Navigate to the Policies page.
Select + New to create a new policy.
In General Enter the following details:
- Display name: MDATP Onboarding Contoso 200329 v100.86.92 or later
Select Recurring Check-in.
Select Save.
Select Packages > Configure.
Select the Add button next to Microsoft Defender Advanced Threat Protection and Microsoft Defender Antivirus.
Select Save.
Select the Scope tab.
Select the target computers.
Scope
Select Add.
Self-Service
Select Done.